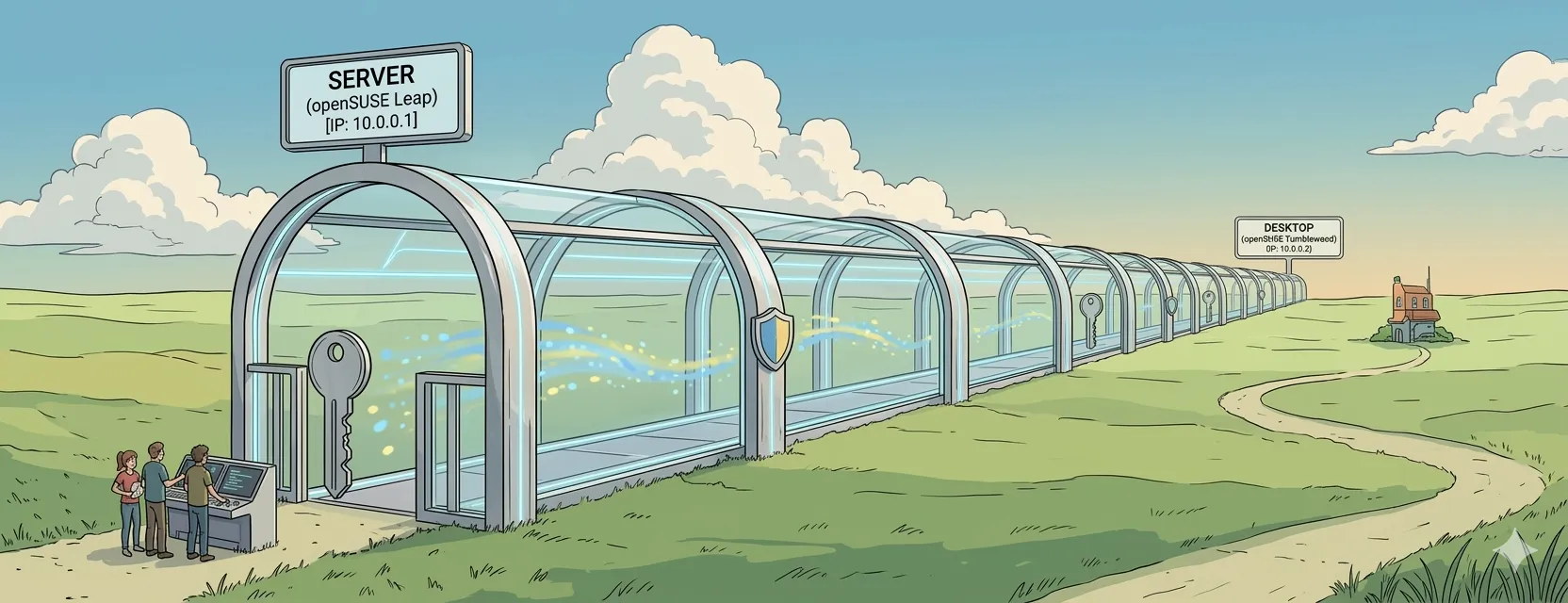
Setting up a secure tunnel doesn’t have to be a headache. In this post, I’ll walk you through how I configured a WireGuard tunnel between my openSUSE Leap server and my openSUSE Tumbleweed desktop.
WireGuard is incredibly fast and lean, making it a perfect choice for connecting remote machines securely. Here is the breakdown of my setup.
Installation and Key Generation
The first step is getting the tools on both machines and generating the cryptographic keys.
# Install the necessary tools
sudo zypper install wireguard-tools
# Create a secure directory for your keys
mkdir -p ~/wireguard && cd ~/wireguard
# Generate private and public keys
wg genkey | tee privatekey | wg pubkey > publickeyServer Configuration (openSUSE Leap)
On the server side, we define the interface and identify the Home PC as a trusted peer.
Edit the configuration file: vi /etc/wireguard/wg0.conf
[Interface]
PrivateKey = <Server_Private_Key>
Address = 10.0.0.1/24
ListenPort = 51820
[Peer]
PublicKey = <PC_Public_Key>
AllowedIPs = 10.0.0.2/32Home PC Configuration (openSUSE Tumbleweed)
On the desktop, we point the tunnel toward the server’s public IP address.
Edit the configuration file: vi /etc/wireguard/wg0.conf
[Interface]
PrivateKey = <PC_Private_Key>
Address = 10.0.0.2/24
[Peer]
PublicKey = <Server_Public_Key>
Endpoint = <Server_IP>:51820
AllowedIPs = 10.0.0.0/24
PersistentKeepalive = 25Bringing the Interface Online
Once the files are saved, you can start the tunnel and set it to launch automatically on boot.
# Start the tunnel
sudo wg-quick up wg0
# Enable it on startup
sudo systemctl enable wg-quick@wg0Securing the Server with Firewalld
To keep things secure, I use a dedicated zone in firewalld for the VPN traffic. This setup allows SSH over the tunnel while rejecting everything else, and it opens the specific UDP port required for WireGuard to communicate.
# 1. Create a new zone for WireGuard
sudo firewall-cmd --permanent --new-zone=vpn
# 2. Reload to make the new zone available
sudo firewall-cmd --reload
# 3. Add the WireGuard interface (wg0) to this zone
sudo firewall-cmd --permanent --zone=vpn --add-interface=wg0
# 4. Allow ONLY SSH in this zone
sudo firewall-cmd --permanent --zone=vpn --add-service=ssh
# 5. Set the "target" to REJECT (blocks everything else in this zone)
sudo firewall-cmd --permanent --zone=vpn --set-target=REJECT
# 6. Open the WireGuard port on the public interface
sudo firewall-cmd --permanent --zone=public --add-port=51820/udp
sudo firewall-cmd --reload